Security is a key feature in every connected product. But the real question is: what do you want to secure? Do you want to protect the Intellectual Property? Or maybe the integrity of your product? Do you want to secure data at rest? And what about data in transit? These and other questions can be answered with a proper threat modeling process so potential threats can be identified and mitigated.
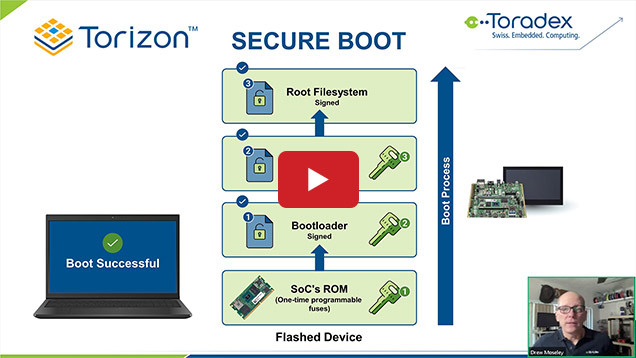
In this webinar, an example of threat modeling to identify the security requirements of an embedded Linux system is discussed, and a wide range of tools and techniques to implement the security requirements is presented, including secure/verified boot, data integrity and encryption, TPM and key management, secure firmware update and patching, secure coding, sandboxing and containers, TEE, mandatory access control (SELinux, AppArmor, etc), authentication, port scanning, and many more!
- Understand why security is important for your product
- Learn how threat modeling can help understand the product's security requirements
- Have an idea of what should be secured in an embedded system and why
- Learn different tools and techniques to improve the security of an embedded Linux system